Reveal security
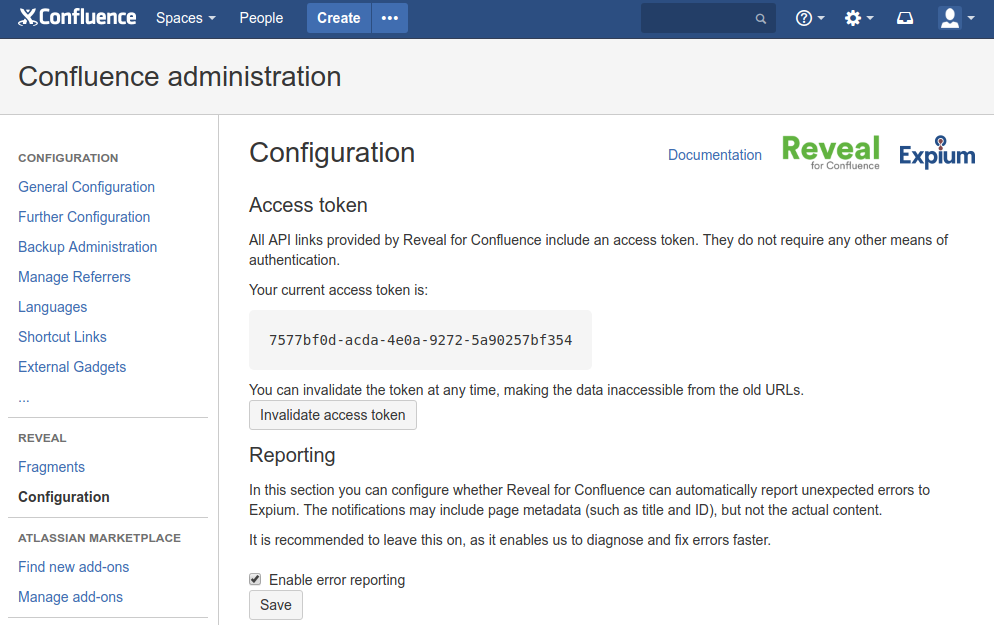
For easier integration, the API endpoints do not require any complex authentication. All the URLs include an access token and can be immediately consumed by any application.
If you suspect the token may have been compromised, it can be easily invalidated and re-created in app configuration. As soon the token is invalidated, all the old URLs using the previous token will become invalid.